Hack the FBI
Genres:
Themes:
Game Modes:
Description from Steam STEAM
A short, tightly scripted hacking adventure revolving around the dangers of power and the vulnerable technology of our modern society. Recruit a team of hackers to save your brother from a vindictive prosecutor, and discover a secret agenda with a global reach.
The game has 20+ beautifully rendered characters, each with their own flaws and motivations. Chat in chatrooms and over instant messenger, snoop on private emails and calendar appointments, scrutinize web browsing habits and purchase histories; NPCs are complete characters, each with explorable computers and visible activities.
A shy analyst struggling not to be labeled by her gender meets a stoic Russian developer trying to make an honest living surrounded by the black market... a manipulative enforcer that cares less about ideology and more about bending others to her will...
A vicious federal prosecutor is railroading your brother with spurious charges. What is he really after? Who is funding the hacker collective that has taken up your brothers case?
There is a core scripted story that spans your brothers desktop to the corridoors of power. Subtle influence and hidden agendas give way to direct action and difficult choices. . Reveal new layers of the story with subsequent NewGame+ playthroughs. As the main story is exposed, threads are left behind for the player to pull and explore at their own pace.
There are many ways to spend time in the game. Explore a hacked system, puzzle and plan over how to locate and infiltrate target, or hang out out and listen to hacker NPCs chatting. But specifically when it comes to hacking a target, there is a sequence that will always occur in some form:
Exploration
Exploration and deduction are large parts of the game. Besides the pure fun of snooping around someone elses digital life, key clues can be discovered that reveal new servers or attack avenues. For example, discovering an email address of "sales@hyperion.net" means not only is there a server at to be investigated, but its probably running a mail server which can potentially be bruteforced, with the username "sales". This kind of passive exposition is a goal of the game, rather than feeding information to the player line by line.A second aspect of exploration is the reconaissance of a server prior to attacking. Once a target is located, its ports must be scanned to enumerate its running services. A more aggressive scan will also list the versions of the different software running. Cross-reference running services with known exploits to find a way in, or if there are no known exploits, you might have to open up your fuzzer analyzer to try and discover a new zero-day exploit. But always ask around the darknet markets first to see if you can buy your way in, either through stolen credentails, or an upgraded version of a hacking program.
Attacking
The actual attacks are not the focus of the game, but when executing a hack, different attacks take the form of puzzles and minigames. Once inside, depending on different factors like your method of intrusion, your skill in the minigame, target defenses, etc, an active trace may have been triggered, in which case you'll need to work quickly to do what you need to do before time runs out. Only the most skilled hackers can infiltrate the top systems undetected.Spending resources
A great designer once described gameplay as "a series of interesting decisions". How you spend your resources should be part of the fun.Resources can be:
- Hardware power (CPU cycles, network bandwidth)
- Money
- Time
- Exploit visibility

Personal computers
Average user PCs won't have many powerful services running, however they almost always contain valuable things like bank account details and juicy personal secrets. To get in you'll need to leverage your malware and phishing skills.Corporate systems
Companies protect their secrets well, due to their valuable nature. Firewalls, antivirus, and active intrusion detection systems are all formidable obstacles to even highly skilled hackers, and their system administrators rarely fall for social engineering. For these advanced environments, you'll need a combination of pure technical skills and raw firepower.Other services
Some servers offer useful things such as email, web hosting, or other support services. While they may not hold monetary value, the user accounts they contain can often be cracked to unmask a targets password, which can be used on more important or secure systems. Not to mention getting file access to all the emails the server holds! Additionally, these machines often have high-spec hardware, a valuable addition to any botnet.
Vulnerability scanning
Portscan a target to enumerate its running services, or aggressively interrogate it to determine their versions.. then browse your collection of exploits for a match, or use what you find to research a new exploit.Fuzzer
Analyze programs for previously undiscovered zero-day vulnerabilities. Trade time and CPU capacity for powerful new attack vectors.Bruteforce
An improperly configured target will allow rapid, semi-random login attempts.. given enough time (and bandwidth) the correct credentials can eventually be guessed!Log deletion
Don't get backtraced! Remember to clear out any logs that might reveal your connection information. Easily automated via a script, or even better, use root access to disable logging outright.Malware
Craft your own malware with a custom payload! Discreetly kill a crucial process, extract a valuable file, or wipe out their entire OS. Add-on modules like packers can sneak your shellcode past antivirus scanners, and stealth modules like log deleters cover your tracks.Proxies
Every hacker needs a network of compromised devices to bounce their connection through.Botnet
Every server you hack can be added to your network of compromised devices. Bandwidth is especially useful for distributed attacks and cryptocurrency mining.
Address book
Keeps track of who, what, where. Automatically stores interesting things like:- Server addresses (and their portscan results)
- Known identities (not necessarily persons)
- Account credentails
Antivirus
Scans files for malware. Keeps you safe, but presence on a target will hinder your own attacks.Can be process-killed, or evaded with a certain cleanroom stealth module.
Background
Rotate through cool backgrounds befitting an leet hax0r such as yourself. Move your own images into the right folder (IRL) and use them in the game!Beacon
You can only fight enemies you can see; get a target to run this and it'll phone home, giving you an address to attack.Browser
Browse the information superhighway, graphically.Bruteforce
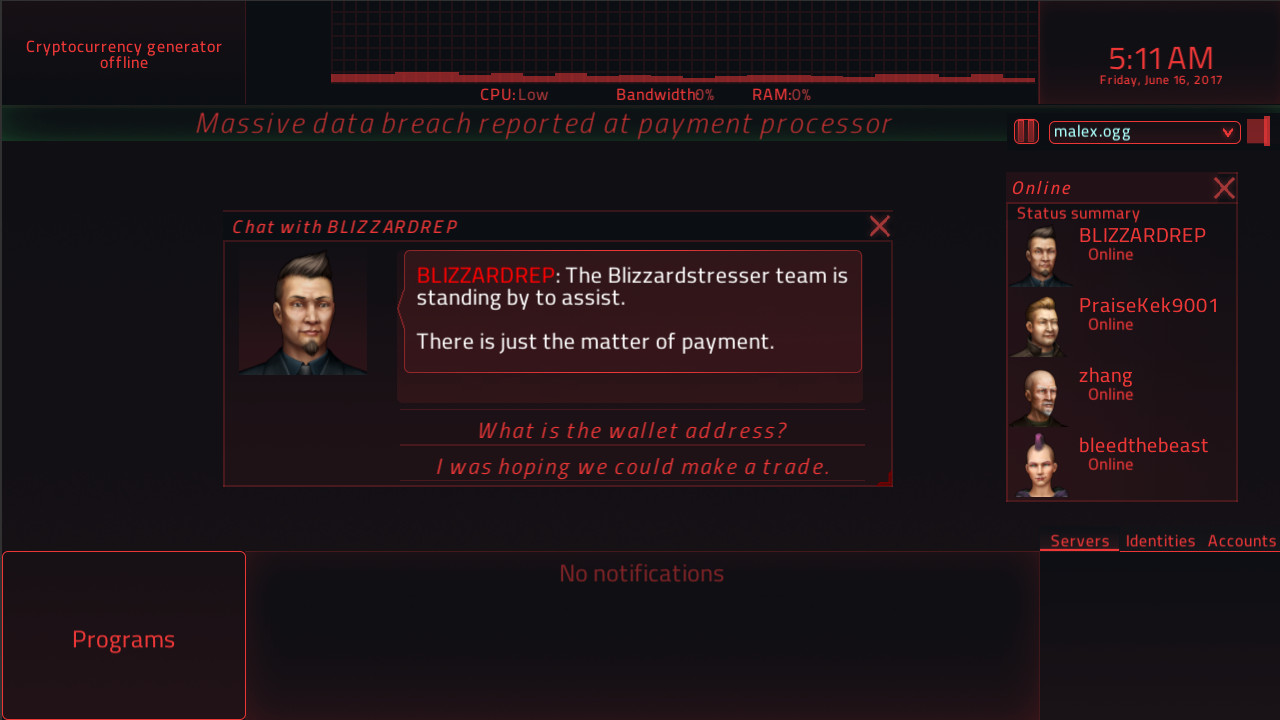
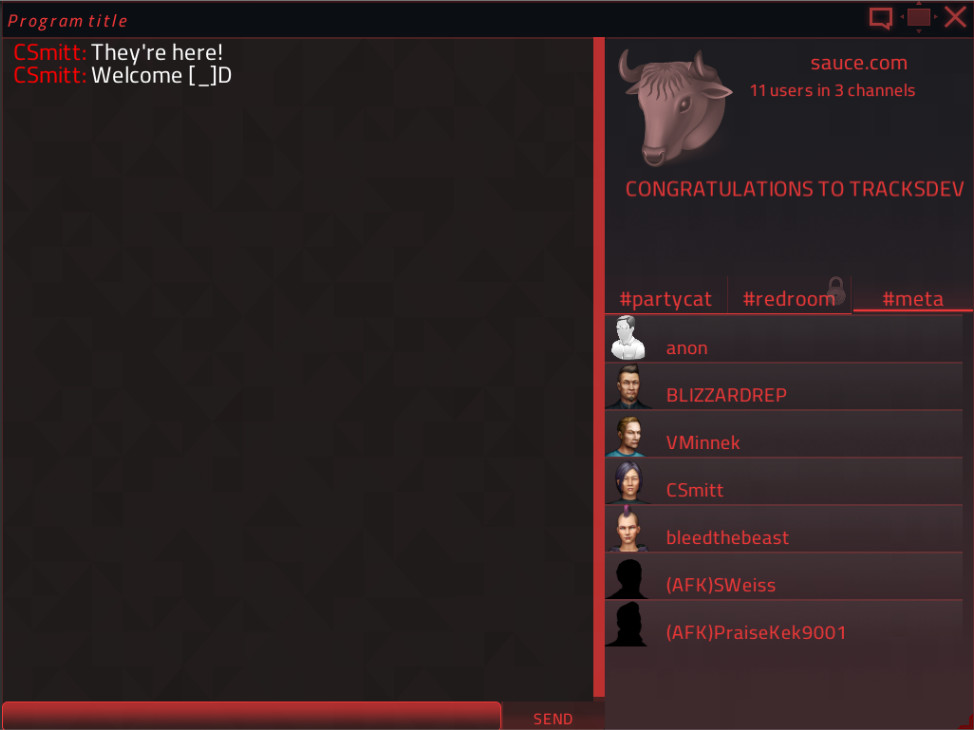
No password? No problem! Force your way in via services like SSH (port 22), SMTP (port 25), or even web page auth (port 80).Chatroom
Chat with AI hackers, stroke moderator egos, maybe get an invite into the password protected back room.Cleanroom
Use this command-line malware lab to build your own executable: choose a payload, crypter, and stealth module. Advanced players can write their own shellcode for ultimate pwnage.Clock
Important for synchronizing attacks with other hackers, pulling off exploits with narrow execution windows, and reminding yourself how little sleep you're about to get.Decrypter
Important files are sometimes encrypted.. but not for long. Graphical minigame to clear memory blocks and help along the decryption process.EmailClient
Send, receive, read emails and attachments.Fuzzer
Don't have an exploit for a target? If you can get a copy of the executable (or even better, the sourcecode) the fuzzer will automatically analyze it for potential vulnerabilities.HardwareMonitor
Keep track of processor usage, bandwidth, and memory capacity. An unexpected spike might indicate you've been compromised...Messenger
Aim to chat with your infosec peeps one on one. Can transfer files. No emojis.Journal
Display currently active tasks, sidequests, and notes.MailServer
Listens for SMTP traffic on a domain. Compromise this and get access to a massive trove of communications.Malware
Broad, abstract category for any program that contains a malicious payload. Payloads can be shellcode scripts, other executables, or simple files that need to be deposited on a target.MusicPlayer
Any good hacker needs a hacking soundtrack.NewsScroller
Get the latest news delivered to your desktop in a minimally intrusive way. Keep up on world developments, and maybe see what you've done in the latest headlines.NMap
Recon a target by finding out what other servers are in its network.OS
Where the magic happens. The one process you really don't want to kill.Phisher
Disguise emails as coming from within a targets social circle. Crucial to getting malware executables into a machine and running.SQL Server
Stores data. Interrogate and retrieve with real SQL commands!SSHClient
Connect to other computers with (or without) the right password.SSHServer
Allows incoming connections from other computers and gives local access privileges.Terminal
Some programs only accept command line input, with no GUI. Advanced players might choose the terminal over a GUI for speed.Text Editor
For editing text, duh.Tutorial Launcher
Run different tutorial programs that teach broad concepts or specific programs.Vulnerability Scanner
An aggressive port scanner, cross references running services with a database of known vulnerabilities.Wallet
Put your processor to work mining cryptocurrency, which can be traded for goods and services.Webserver
Listens on port 80 for web requests to serve up.
Can I play this even if I'm not great at computers?
Of course! This is a VIDEOGAME first, and hacking game second. There will be tutorials for different aspects of the game. But you'll still have to get good.
Do I need to know programming/is this a programming game?
This is not a programming game, but some aspects of it do use limited SQL, as well as the ability to write your own shellcode scripts, but the game can still be won without mastering these things.

Reminder that this game is in its unfinished form! With any luck, a lot will change between now and when its finally released. But until then, remember that there will be:
- bugs
- unfinished features
- missing content
- balance problems
- everything else that goes with a game thats currently in development
Description from IGDB IGDB
Basic Info
Additional Information
Платформы 1
Genres 5
Themes 2
Game Modes 1
No Companies Available
Company information for this game hasn't been loaded yet.
Keywords