Echoes of MK-ULTRA
Genres:
Themes:
Game Modes:
Description from Steam STEAM
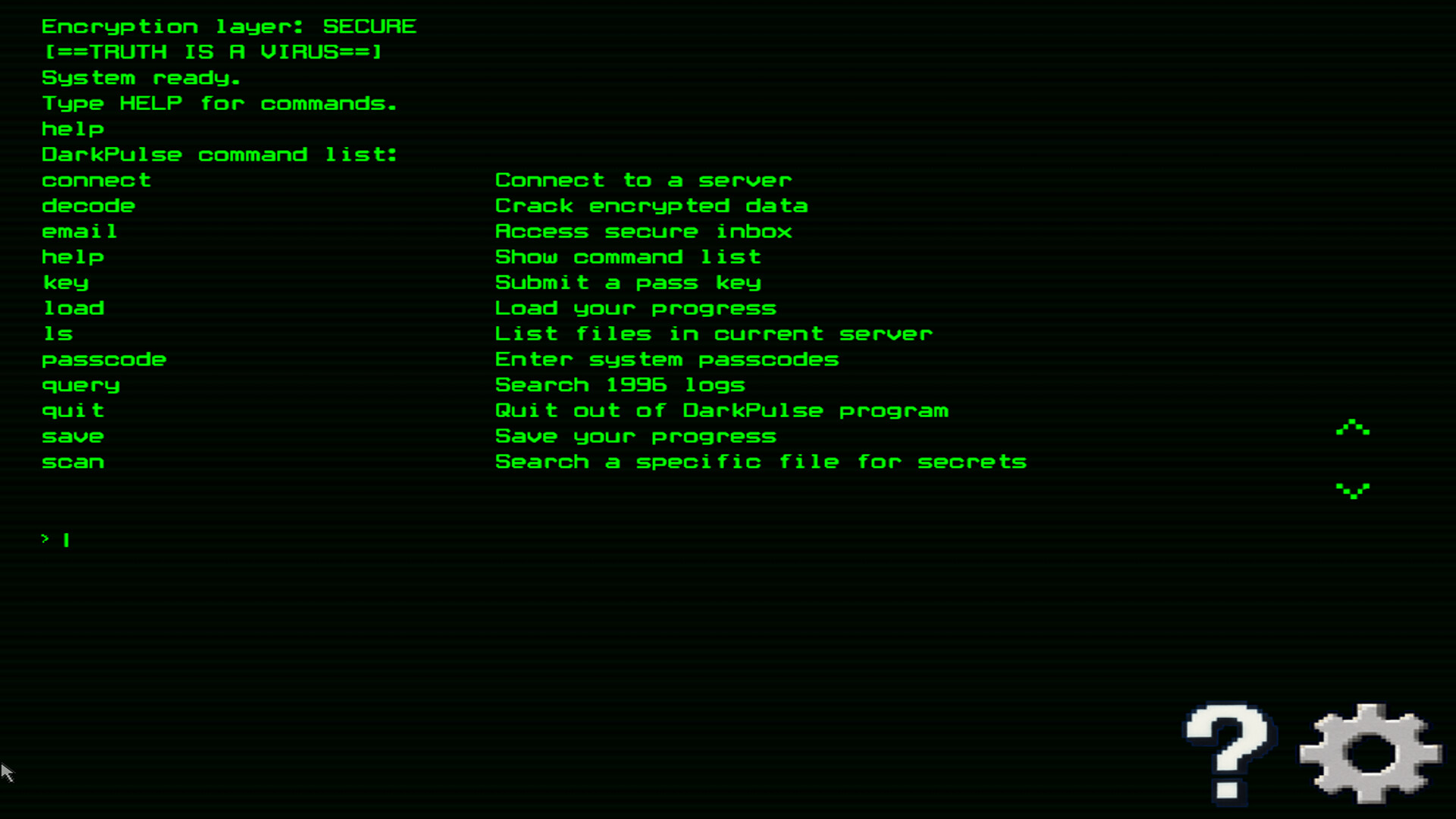
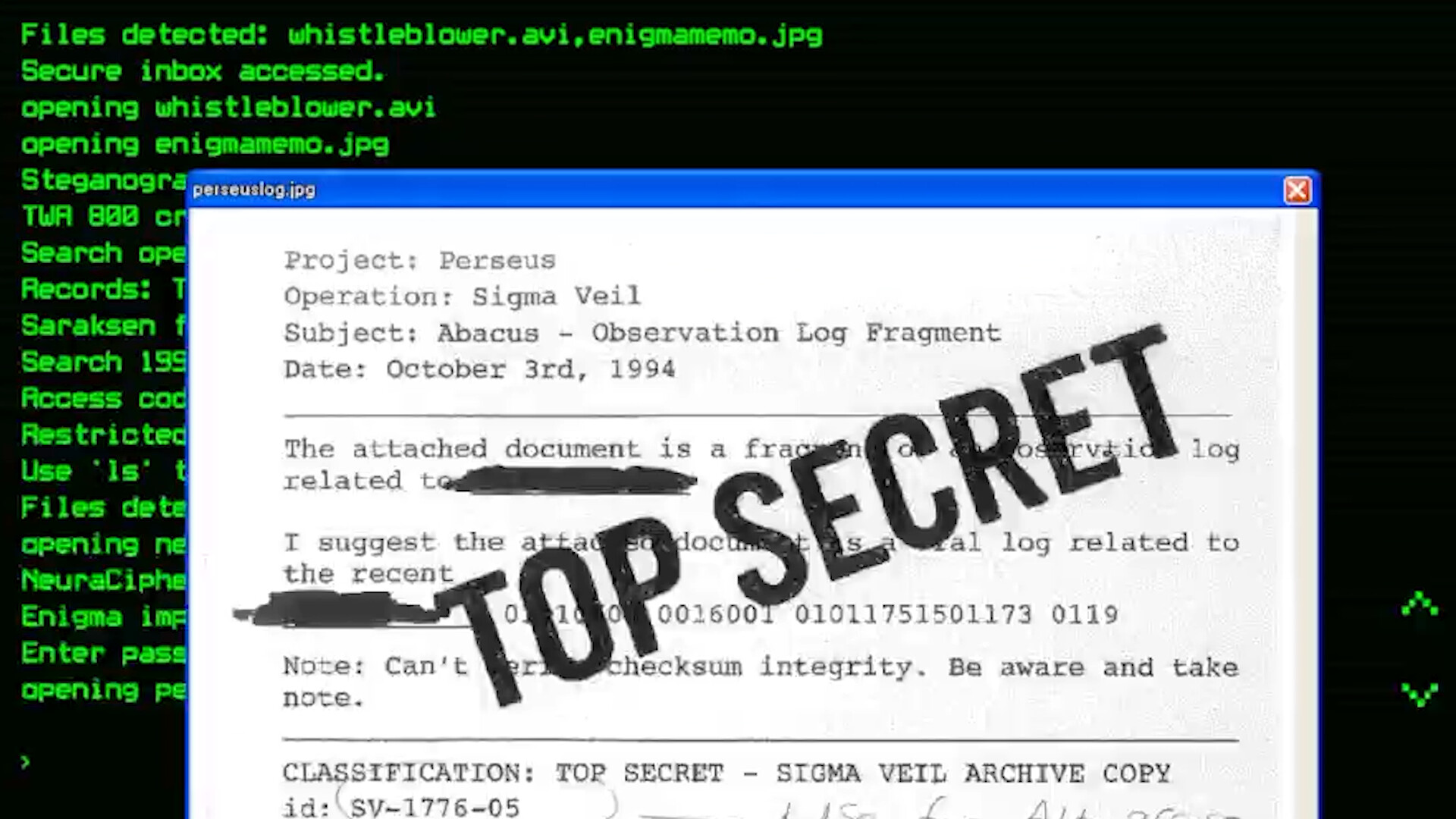
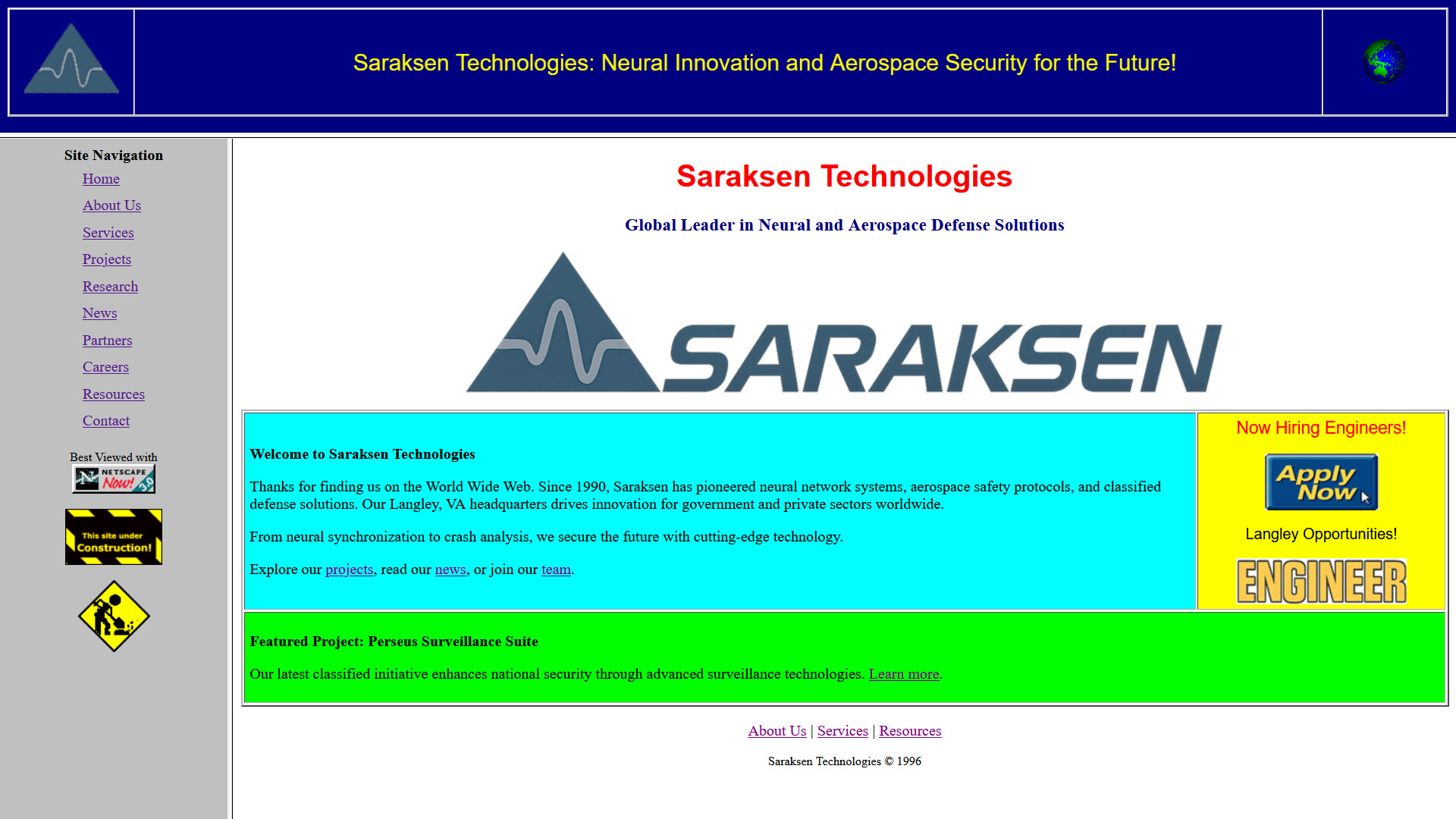
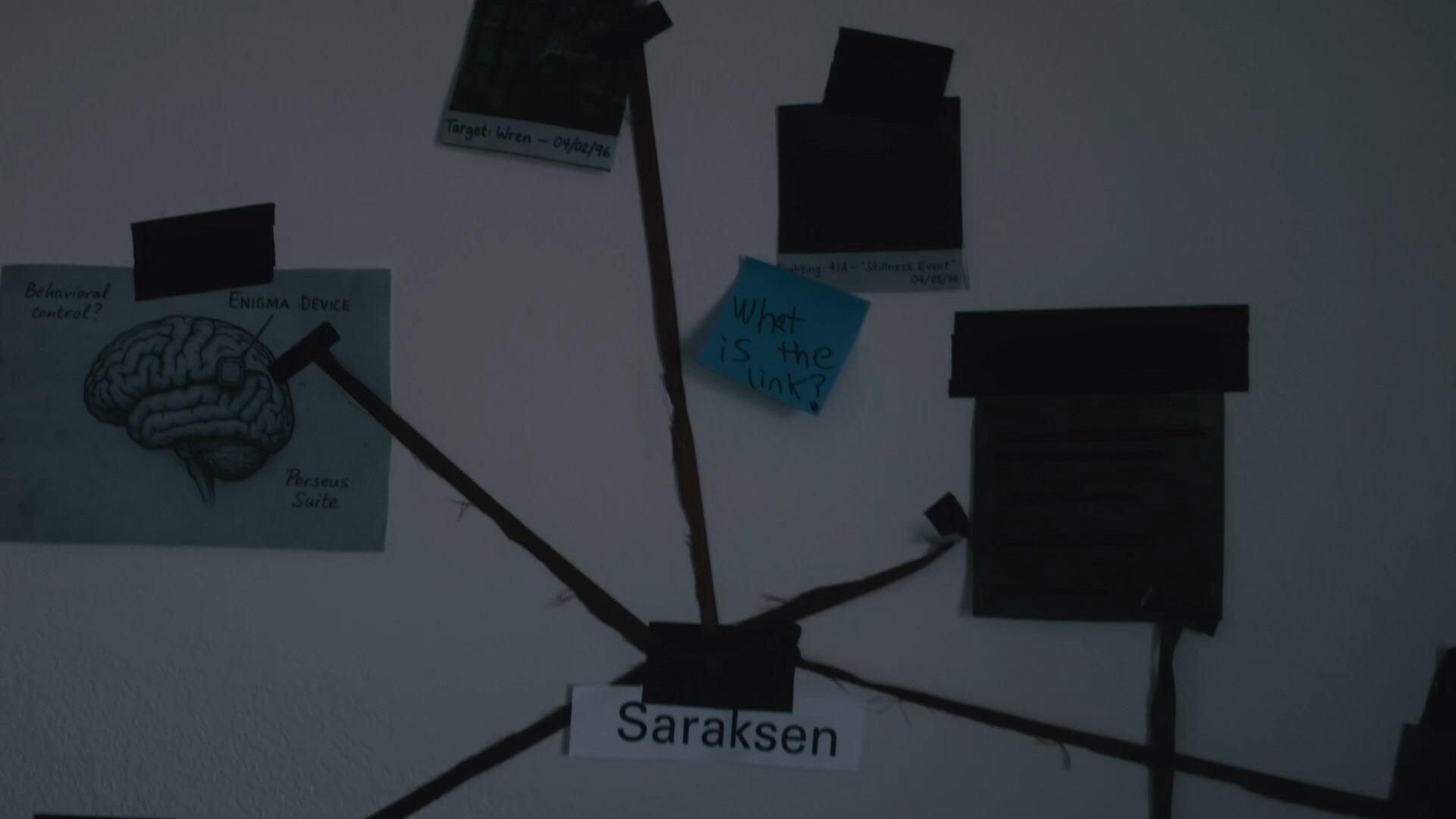
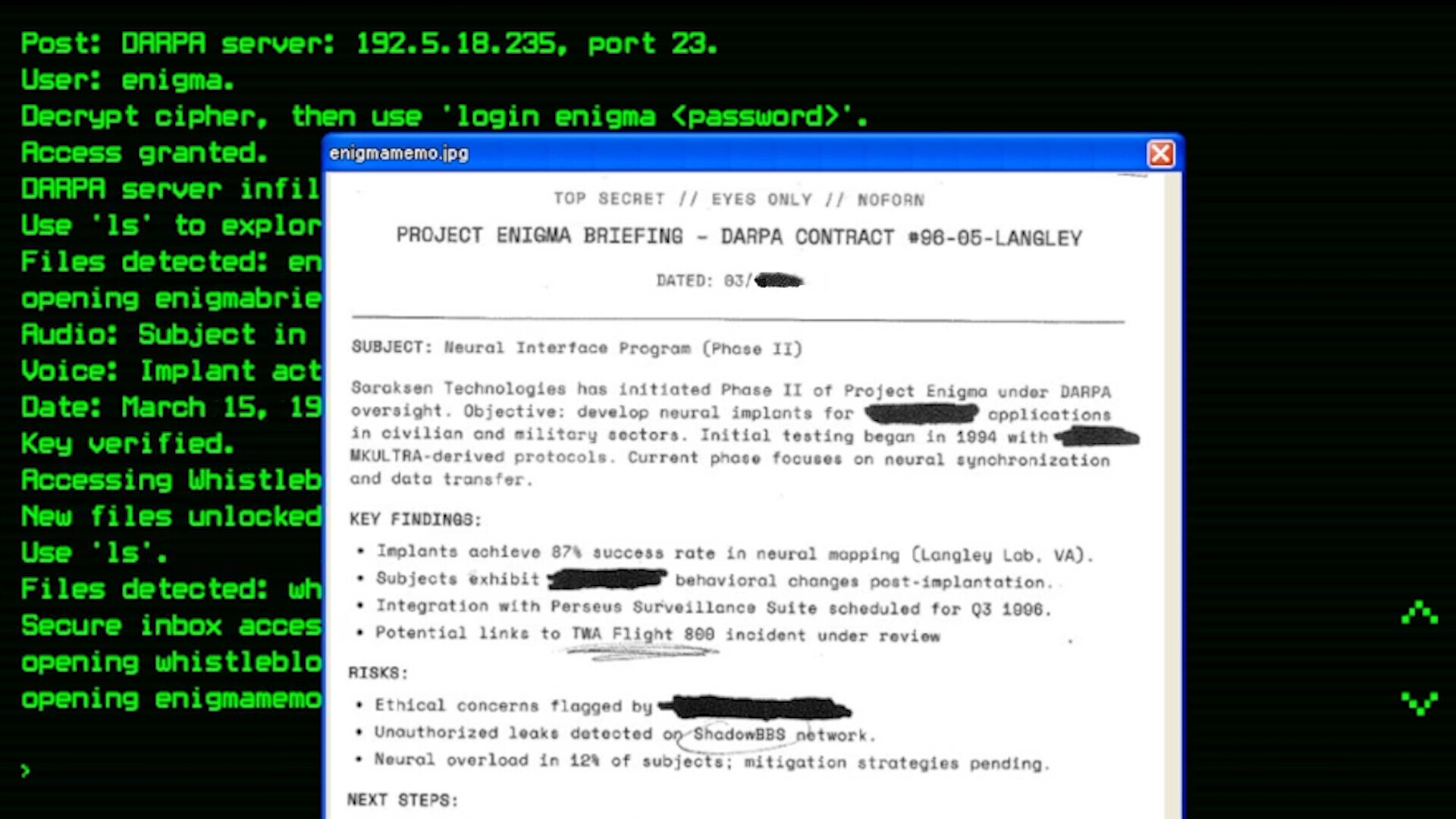
CLASSIFIED: DARPA ARCHIVE LEAK – EYES ONLY // NOFORN Document ID: DP-96-03-SHADOW Date: March 16, 1996 Status: DECRYPTED – ORIGIN UNKNOWN SUBJECT: Unauthorized Software – “Enigma Protocol” WARNING: Possession of this program violates Title 18, U.S.C. Distribution may trigger surveillance escalation. In the neon static of 1996, a rogue signal fractures the grid. You intercept DarkPulse —a black-market terminal ripped from DARPA’s vaults. Meant for cyberwarfare. Now it’s in your hands. You are the ghost in the machine. At first, it’s simple: type commands, breach servers, stay hidden. But encrypted whispers leak from corrupted files. Corporate espionage, blacksite labs, and a buried protocol the world was never meant to see. The story doesn’t stop at the screen—clues bleed into reality: phone numbers, websites, scattered coordinates. This is an ARG for those who still remember how to get lost online. Saraksen Technologies is watching. Every input risks exposure. The modem screams. The system pulses. Your next move matters. Will you ignite the signal, or vanish into digital static? ⚠️ FEATURES: Terminal-Based Hacking : Type real commands, crack systems, evade detection. DARPA-Origin Tech : Use DarkPulse , a stolen prototype built for neural infiltration. ARG Integration : Solve puzzles beyond the game—track hidden clues across the real internet. Multimedia Immersion : Decode corrupted text logs, audio surveillance, and video fragments. Choice-Driven Ending : What you uncover—and what you choose to share—alters everything. OPERATIVE WARNING: The truth is a weapon. Data persists. So do secrets. ADDENDUM: [REDACTED] signals detected. More to come. END OF TRANSMISSION DESTROY AFTER READING
Description from IGDB IGDB
Basic Info
Additional Information
Платформы 1
Genres 3
Themes 2
Game Modes 1
No Companies Available
Company information for this game hasn't been loaded yet.
Keywords